Read about the latest cybersecurity news and get advice on third-party vendor risk management, reporting cybersecurity to the Board, managing cyber risks, benchmarking security performance, and more.
Insights blog.

Critical Vulnerabilities Discovered in Automated Tank Gauge Systems
Bitsight TRACE explores several critical vulnerabilities discovered in ATG systems and their inherent risk when exposed to the Internet.
Third party risk management is trending following major data breaches affecting organizations through their vendors. But what is TPRM?

Attacks targeting operational technology & industrial control systems are rising while many cut security budgets. Comprehensive strategies and monitoring are essential now more than ever.

With economic sanctions being levied by the US against Iran and a trade war heating up with China, some security experts are cautioning that attacks targeting US critical infrastructure may be inevitable. Are electric utilities prepared to defend themselves and their facilities against these attacks?

Bitsight was named a Leader in The Forrester Wave: Cybersecurity Risk Ratings Platforms, Q2 2024 for a third consecutive time.

Dive into a significant cybersecurity scare that could have led to widespread chaos, highlighting the vulnerabilities that were exposed and the swift actions taken to prevent disaster.

Security leaders have got to be ready to direct the conversation on security in a manner that resonates with directors. Here's how.

Every organization handles security differently, based on their needs and internal structure — but in some mid-sized and large companies, both the chief information officer (CIO) and the chief information security officer (CISO) are involved.
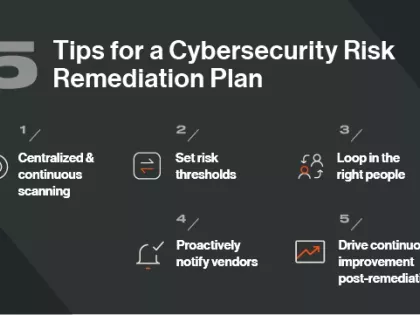
Does your organization have a cybersecurity risk remediation plan? Follow these 5 tips for crafting one.

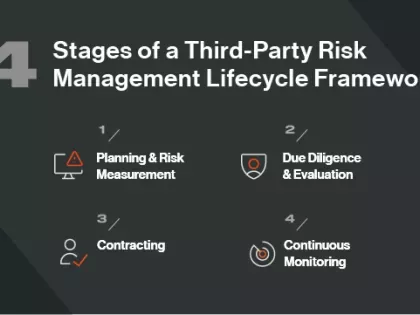
The vendor lifecycle management process involves understanding and remediating third-party risk at every stage of the relationship, from onboarding to offboarding.

Here are some key tips for presenting the outcomes tracked by exposure management in a way that will be most helpful to the board and business stakeholders.

Bitsight’s global, advanced scanning and detection capabilities provide insight into many actively exploited vulnerabilities that others just can’t touch. Explore how we do it.

Email is a well-known and widely used attack vector for malware distribution, phishing, and many other types of threats.

If you’re experiencing frustrating delays and procedural roadblocks during your vendor management process, you’re not alone. Security managers are seeing an increase in the number of third-parties integrating with their business, and Gartner reports that “60% of organizations are now working with more than 1,000 third parties”.

Cyber risk mitigation and remediation are often talked about in the same terms. But they are different. Learn how you can optimize both.

With the right mindset and governance, visibility into enterprise exposures can push priorities all the way up into the strategic realm of enterprise risk management—whilst enabling a threat informed defense posture.