Read about the latest cybersecurity news and get advice on third-party vendor risk management, reporting cybersecurity to the Board, managing cyber risks, benchmarking security performance, and more.
Insights blog.

Critical Vulnerabilities Discovered in Automated Tank Gauge Systems
Bitsight TRACE explores several critical vulnerabilities discovered in ATG systems and their inherent risk when exposed to the Internet.

Penetration tests (a.k.a. pen tests) are point-in-time cyber risk assessments. They allow IT and security professionals to assess the adequacy of security controls, including intrusion detection and response systems, and identify weaknesses that need attention.

Since our foundation in 2011 as the first company to provide a rating for measuring a company’s cyber security, Bitsight has become the world-leading security ratings provider. Bitsight is used around the world by industry leaders, country governance systems, as well as smaller organizations alike to take control of their cyber footprint, using safe and objective rating techniques. What does Bitsight do to stand apart from others in the security industry?

Read this blog to discover how tackling technical debt can transform your cybersecurity strategy, boost efficiency, and ensure compliance.

Before Crowdstrike caused the world to melt down for a few days, the talk of the security town was a recent OpenSSH vulnerability. Let's revisit CVE-2024-6387.

Dive into the SANS CTI Survey 2024 to find out why threat hunting is now the top CTI use case, and the rise of CTI reports importance. Read more now.

Trust Management Hub gives GRC teams a centralized & scalable way to manage & share critical security questionnaires and documentation.

Bitsight's analysis of the CrowdStrike outage and timeline mysteries.
Organizations today aren’t single entities—they are interconnected networks of third parties. And while third party relations are critical for success in most businesses, they also leave data more vulnerable to exposure from bad actors. Because of this, vendor risk management (VRM) is becoming an even more important business practice.

This post will focus on recent developments in Bitsight Groma.

We’re closely analyzing the cause of–and response to–the CrowdStrike global incident to better understand how organizations can understand and mitigate risk.
Curious about software vulnerabilities and their fixes? Check out my latest blog on KEV exposures and common weaknesses for surprising insights!

Learn the definition of IT risk management & the steps your organization can take to protect itself from cybersecurity risk across your business ecosystem.

Economic pressures push CISOs to justify resources and consolidate tech for data, operational, and cost efficiency. Bitsight aids with comprehensive risk data and solutions.
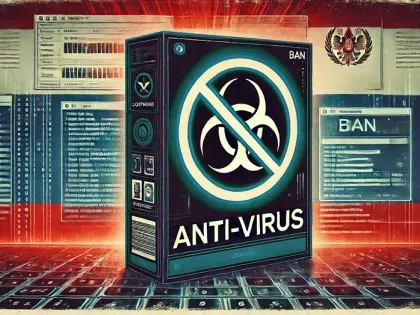
How will the prohibition of Kaspersky Lab, Inc. impact global users? Read our analysis of the prevalence of Kaspersky products used by organizations around the globe.

How do you determine who is a 'critical supplier'? Delve into practical strategies to identify crucial partners and ensure compliance with NIS2 requirements.