Read about the latest cybersecurity news and get advice on third-party vendor risk management, reporting cybersecurity to the Board, managing cyber risks, benchmarking security performance, and more.
Insights blog.

Critical Vulnerabilities Discovered in Automated Tank Gauge Systems
Bitsight TRACE explores several critical vulnerabilities discovered in ATG systems and their inherent risk when exposed to the Internet.

For the first time ever, Diligent and Bitsight have partnered to see just how well the board level effort is translating into reducing Cyber Risk for their company.

Bitsight's leading analytics and workflows allow investors to effectively reduce cyber risk across their portfolio. Doing so does not require cyber or technical expertise - allowing investors to focus on what they do best.

La mise en œuvre d'un plan de réponse aux incidents de cybersécurité peut vous aider à gérer efficacement un cyber-événement, à réduire les perturbations de votre activité et à garantir la conformité.

Discover the complexities of exposure management in the cybersecurity landscape, as we dissect the acronyms and delve into the fundamental need for better visibility into asset states.

We’re back again with a monthly-ish blog reflecting on major goings on in the security world.

While all areas of risk management involve blind spots, supply chain risk management might be the murkiest. To be effective in this field, risk professionals must account for risks from a wide variety of sources, from bad password management to geopolitical upheaval. Supply chain risks can be difficult to detect, unpredictable, and fast-moving.

Explore the concerning cybersecurity landscape in Australia's finance sector, marked by major data breaches and deficiencies in notification procedures, highlighting critical vulnerabilities and pressing challenges.

What is adaptive security? Explore the benefits of this approach to cyber risk reduction and how your organization can get started.

Key Risk Indicators (KRIs) können dabei helfen, Cyberrisiken zu überwachen und zu kontrollieren. Aber auf welche KRIs sollten Sie sich konzentrieren?

Les indicateurs clés de risque (KRI) peuvent aider à surveiller et à contrôler les cyber-risques. Mais sur quels KRI devez-vous vous concentrer ?

Tim Grieveson from Bitsight discusses strategies for managing Shadow IT, emphasizing the need for cybersecurity leaders to balance security and convenience.

A monthly or quarterly report is a great way to summarize a SOC’s performance and uncover insights for executive leadership. But as a security and risk manager or executive, what information should you request from the managers who report to you?
Bien que les évaluations de sécurité soient un excellent moyen de démontrer que vous prêtez attention à la cybersanté de l'organisation, vous devez également montrer que vous adhérez aux meilleures pratiques industrielles et réglementaires en matière de sécurité informatique et que vous prenez des décisions éclairées à long terme. . Un cadre de cybersécurité peut aider.
Während Sicherheitsbewertungen eine gute Möglichkeit sind, zu zeigen, dass Sie auf die Cyber-Gesundheit des Unternehmens achten, müssen Sie auch zeigen, dass Sie sich an branchenübliche und behördliche Best Practices für die IT-Sicherheit halten und fundierte Entscheidungen auf lange Sicht treffen . Ein Cybersicherheits-Framework kann helfen.
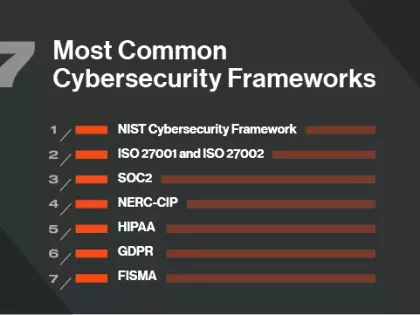
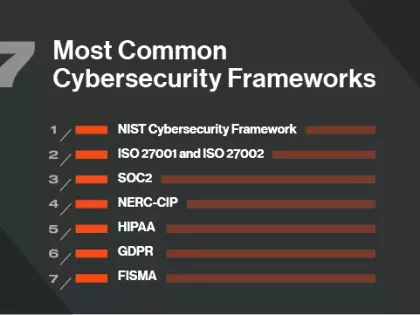
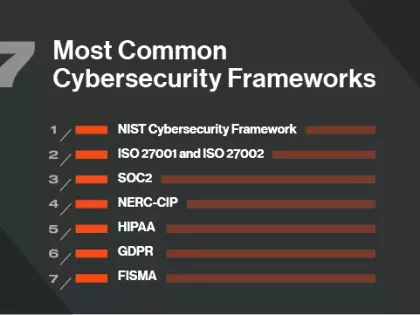
While security ratings are a great way to demonstrate that you’re paying attention to the cyber health of the organization you also need to show that you’re adhering to industry and regulatory best practices for IT security and making informed decisions for the long-term. A cybersecurity framework can help.