Read about the latest cybersecurity news and get advice on third-party vendor risk management, reporting cybersecurity to the Board, managing cyber risks, benchmarking security performance, and more.
Insights blog.

Critical Vulnerabilities Discovered in Automated Tank Gauge Systems
Bitsight TRACE explores several critical vulnerabilities discovered in ATG systems and their inherent risk when exposed to the Internet.

Written with the assistance of Dan Dahlberg, Ethan Geil, and Ross Penkala.

Onboarding third-party vendors that will have access to your network and data can have dire consequences if you don’t have the ability to gauge vendor risk. In a recent joint survey between Bitsight and IDG Research Services, more than 260 IT managers and professionals, nearly 70% said they were “extremely concerned” or “very concerned” about the security risks posed by third-party vendors and suppliers. Another study found that nearly two-thirds of breaches involve a third party.

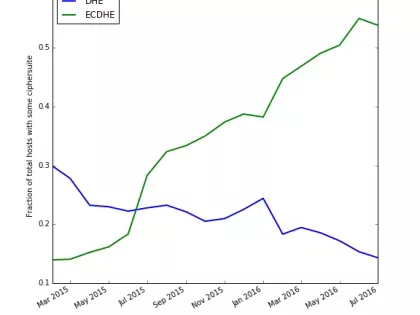
Bolek is a recent malware from the Kbot/Carberp family. We first heard about this malware from the cert.pl blog post in May 2016, and since then, a few others have published additional information about it (links below).

Last month, email giant Yahoo announced the compromise of 500 million user accounts—which is being called the largest breach from a single site in history. The breach compromised names, email addresses, telephone numbers, dates of birth, passwords, and some encrypted or unencrypted security questions and answers.

Ponemon Institute’s study, Data Risk in the Third-Party Ecosystem, highlights the challenges that companies face in protecting sensitive and confidential information shared with third parties.

Security Ratings are still a relatively new phenomenon. As a result, many security and risk professionals are still familiarizing themselves with how ratings work, the data used to compute ratings, and how ratings are put into action. We expect this education to continue: consumer credit scores are always changing and after many years, people are still constantly coming up to speed with the multitude of factors that affect their score.

Like many technical industries, cybersecurity has a lot of specialized lingo. But there are two dozen cybersecurity terms in particular that are critical to understand. We’ve defined them here (in alphabetical order) and linked to a few articles that may help you better understand them along the way.

Ransomware has been all the talk lately in the security industry- and deservedly so. These attacks have surged in the last year: hospitals, banks, and local police departments have all been infected with ransomware. Organizations have been paralyzed for days and weeks as a result of ransomware infections. In March, a MedStar Health clinic in Baltimore reportedly turned away patients and had trouble accessing electronic medical records. In a separate incident, the University of Calgary paid a $20,000 ransom earlier this year after malware encrypted the university's email servers. In addition to a financial loss for organizations that decide to pay ransoms, these attacks have the potential to cause severe operational disruptions for companies.

From time to time we have the opportunity to sinkhole domains that have an high volume of traffic and are part of a mobile device botnet. In the beginning of July we registered a domain that we found to be part of the AndroidBauts family with over 550,000 devices for a 24h period, affecting mostly India and Indonesia from a total of 216 countries. The piece of software that triggers this traffic was present in four (already removed) Google Play Store applications.

Since our foundation in 2011 as the first company to provide a rating for measuring a company’s cyber security, Bitsight has become the world-leading security ratings provider. Bitsight is used around the world by industry leaders, country governance systems, as well as smaller organizations alike to take control of their cyber footprint, using safe and objective rating techniques. What does Bitsight do to stand apart from others in the security industry?
Vendor risk management (VRM) is a very broad category that encompasses all the measures an organization may take to prevent issues or business disruptions that arise due to vendor and third party relationships. Legal issues, past performance, and creditworthiness are some of the VRM issues small companies review most frequently—but cybersecurity should not be pushed to the back burner.

You’ve likely heard your fair share of mortifying headlines involving IT vendor management. Many of the highly publicized breaches in the last several years occurred simply because the companies did not follow basic best practices for IT vendor risk management (VRM).
A number of leading torrent websites have gone offline recently, drawing attention again to the use of torrents to share copyrighted material. But the absence of these sites doesn’t mean torrents have stopped. Torrenting is a peer-to-peer technology that doesn’t have a single point of failure. Just because some sites have gone down, doesn’t mean you don’t have to care about torrents on your network. In this post, I want to look at the good, the bad, and the ugly of torrents.

Even with every safeguard in place, it’s simply impossible to avoid all cybersecurity breaches. That being said, there are things you can do to lower the chance of a catastrophic one happening in your organization. By looking at a few recent attack vectors and what can be done to mitigate the risks these companies weren’t prepared for, you can help make sure your organization is prepared for a possible cybersecurity breach.

While cybersecurity insurance is a relatively new line of service in the industry (it’s only been around for the last 10-15 years), it is currently the fastest-growing form of insurance. And it’s no wonder—today, a data breach at a large company could cost hundreds of millions of dollars. Spurred on by recent increases in breach activity that have resulted in direct consequences and major costs to companies in every industry, more and more organizations are looking to transfer some cyber risk to insurance companies.
What does cyb
What does cyb