Read about the latest cybersecurity news and get advice on third-party vendor risk management, reporting cybersecurity to the Board, managing cyber risks, benchmarking security performance, and more.
Insights blog.
Slicing through CISA’s KEV Catalog

Slicing through CISA’s KEV Catalog
Dive into the critical insights of CISA's Known Exploited Vulnerabilities (KEV) Catalog with Bitsight’s latest blog! Discover how KEVs, which signal urgent cybersecurity risks, are being tracked and mitigated across industries. Learn why addressing these vulnerabilities quickly is vital and how it impacts organizational security.

In his 2015 State of the Union Address, President Barack Obama mentioned the importance of improving America's cybersecurity and what he believes it will take to make it happen. Below is a review of the most interesting statements and initiatives mentioned in the address or recent media coverage, and the potential impact each could have on American Information Security.

In 2014, Cyber Insurance saw record growth. In fact, in a recent white paper from Advisen, their buyer penetration index showed a five-fold increase in insurance purchases from 2006 to 2013, demonstrating that many organizations have recognized the value in outsourcing corporate cyber risk. Naysayers, however, warn that this move does not make companies more secure and allows organizations to ignore the behaviors and issues that are creating security risks in the first place.

During last month's FS-ISAC webinar, Home Depot, the SEC and Increasing Board Oversight: Why Metrics Matter More and More, Bitsight CTO and Co-Founder Stephen Boyer answered questions from attendees about why using IT security metrics is more important than ever before. He also performed a live demo of Bitsight Security Ratings to show how to prove that security ratings work.

As you've heard by now, Sony Pictures suffered a major breach in November, and is still feeling the consequences of it. The FBI warned that other companies could be attacked with similar malware, but that isn't the only reason you should care about this event in particular.

During last month's SANS webinar, Quantifying Security Performance: The What, Why and How of Security Ratings, Bitsight CTO and Co-Founder Stephen Boyer answered questions from attendees. Here are some of the most interesting questions people posed, and our answers for each one. There are also two clips from the webinar recording.

Last October the world was alerted to Poodle, a vulnerability on websites and servers running SSL 3.0. Acting as a "man in the middle," would-be attackers could compromise the secure connection between a browser and a website, and inject JavaScript that enabled them to view these communications, stealing unencrypted data and manipulating traffic flow. The apparent fix at the time was to upgrade from SSL 3.0 to TLS, but new research suggests this may not be the case.

Bitsight has released new capabilities and features in the Bitsight Security Ratings portal to widen the data breadth offered to customers and give more detailed, granular performance analytics on specific risk vectors. These changes are available to all enterprise, team, and individual tier customers today.

Ever since the JPMorgan Chase breach was made public, companies have been watching closely to see the aftermath, the bank's course of action, and any best practices that may be developed as a result.

Third party breaches have become a common occurrence in the last year. From Target to Home Depot and Goodwill, major organizations have been compromised from vulnerabilities present in their extended network ecosystems. Compounding fears surrounding third party vulnerabilities, the last year has also seen no less than three major security flaws affecting basic internet protocols. The first two, Heartbleed and Bash, grabbed media headlines and left businesses scrambling to ensure they weren't left vulnerable. Just this week, another major security flaw dubbed Poodle was uncovered by security researchers. This bug affects SSL v3, a widely used protocol to secure communications over the internet. With growing concern about third party security and the seemingly neverending revelations of internet bugs, organizations are left wondering how they can better gain visibility into the vulnerability of their third parties when it comes to basic configuration hygiene.

Last week we wrote about how to assess your risk and reduce your exposure when it comes to Shellshock. While all other products and vendors are helping customers discover Shellshock within their own environment, we uniquely help customers understand whether the vulnerability exists within their supply chain. Supply chain oversight is so fundamental that the Federal Financial Institutions Examination Council has already issued a warning to banks regarding their third party service providers, urging them to assess risk and “execute mitigation activities with appropriate urgency.”
The security community is abuzz with the news of the latest vulnerability to sweep the internet. Early yesterday morning, details about the Bash security bug, also called Shellshock, started to emerge, putting companies on high alert about the threat experts are calling “Bigger than Heartbleed.”

There is no denying that cyber security issues have captured headlines over the course of the year. From the highly public Heartbleed bug to major data breaches affecting some of the largest names in business, there has been increased focus on data security. As we have noted in previous posts, in the wake of these events and in the face of new threats, cyber insurance has emerged as a viable option to transfer the risk of financial losses related to data loss. In just the past week a White House official went as far as to say that cyber insurance will be standard for businesses by 2020, just as property or liability insurance is now. But as the cyber insurance market continues to grow, how will large scale breaches affect the industry?

ISACA and the Institute of Internal Auditors (IIA) recently released a report emphasizing the board’s role in overseeing security risk management. In particular, the report mentioned management of third party risk, arguing that boards should ask tougher questions about third party security. According to an IIA survey, only 14 percent of board members said they were actively involved in cyber security oversight. Even though the SEC has asked board members to get involved, 58 percent of board members admit that they should be doing more. If you’ve struggled to get your board to become engaged in your security risk management efforts, particularly related to third party risk, now is the right time to make them aware.

Data breaches at higher education institutions are becoming more and more common, putting them near the top of the list of industries most affected by cyber security risks. Hackers target .EDU networks because they tend to be left wide open for attacks, either because the schools fail to prepare against such intrusions or because network users fall victim to vicious phishing scams. As our latest Bitsight Insights report revealed, university security teams juggle diverse IT infrastructure needs and unique challenges, including BYOD culture and multiple network access points. This leads to a major slump in security performance throughout the school year. So how can universities overcome these challenges?
It is no secret that America's colleges and universities hold a wealth of personal and sensitive information that is frequently targeted by cybercriminals, as evidenced by some public data breaches in the past year affecting major universities. Today we at Bitsight published our quarterly Bitsight Insights report that analyzes the security performance of higher education insitutions in America. We conducted a thorough analysis of the largest and most prestigious collegiate athletic conferences in the nation: the ACC, SEC, Pac 12, Big 10, Big 12 and Ivy League. The member schools of these athletic conferences are large to medium sized universities that give a strong representative sample of the higher education industry in the United States, encompassing a student population of 2.25 million and a network space of more than 11 million IP addresses.
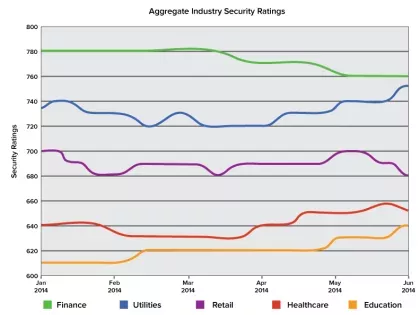
By analyzing the aggregate Security Ratings
By analyzing the aggregate Security Ratings