Read about the latest cybersecurity news and get advice on third-party vendor risk management, reporting cybersecurity to the Board, managing cyber risks, benchmarking security performance, and more.
Insights blog.

Critical Vulnerabilities Discovered in Automated Tank Gauge Systems
Bitsight TRACE explores several critical vulnerabilities discovered in ATG systems and their inherent risk when exposed to the Internet.

SOX compliance requires companies to focus on 7 critical areas: from internal controls to cybersecurity measures. Find a full checklist for SOX compliance.

Learn GDPR Compliance 101: Understand key principles, requirements, and steps to ensure data protection, avoid penalties, and build customer trust globally.

If you operate in specific sectors, cybersecurity maturity is more than a best practice, it’s a regulatory requirement. These regulations are complex and constantly changing. To help you better understand your organization's regulatory environment and the standards and controls they stipulate, let's break down key cyber compliance regulations by industry.

Discover how Bitsight and Glass Lewis integrate cybersecurity into ESG, enhancing transparency, resilience, and trust for corporations and investors.

Discover insights and recommendations to help your organization stay ahead of SOC 2 as part of your overarching cybersecurity compliance strategy.

We asked the Institut Luxembourgeois de Régulation (ILR) about NIS2 and what does it mean in practice. Here are their answers.

Understanding DORA: a key EU regulation enhancing financial sector resilience. Learn its 5 pillars, compliance deadline, and steps to fortify ICT security.

In this Q&A, CNCS shares valuable insights into the challenges, requirements, and best practices surrounding NIS2 compliance.

METI announced its intention to implement a cybersecurity rating system for companies by fiscal year 2025. Here are the key aspects of the planned system.

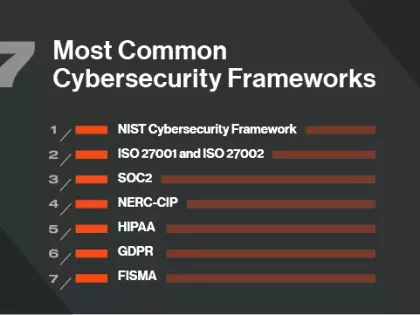
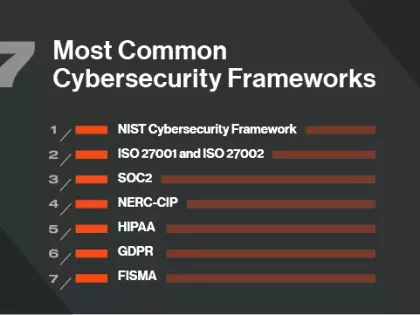
Security risk managers often face a lot of the same roadblocks, even if they’re managing programs of different sizes or in different industries. Basing security practices on well-known, and sometimes government-regulated cybersecurity models will mature your program to overcome process inefficiencies.

The NIS2 Directive recognizes this and has placed a significant emphasis on supply chain security. But what does this mean for your organization? Let’s break it down.

It's proxy season, and investors want information from companies about cyber risk. Investors are leveraging Bitsight’s data analytics to better understand the risks of their investments.

Explore the concerning cybersecurity landscape in Australia's finance sector, marked by major data breaches and deficiencies in notification procedures, highlighting critical vulnerabilities and pressing challenges.
Bien que les évaluations de sécurité soient un excellent moyen de démontrer que vous prêtez attention à la cybersanté de l'organisation, vous devez également montrer que vous adhérez aux meilleures pratiques industrielles et réglementaires en matière de sécurité informatique et que vous prenez des décisions éclairées à long terme. . Un cadre de cybersécurité peut aider.
Während Sicherheitsbewertungen eine gute Möglichkeit sind, zu zeigen, dass Sie auf die Cyber-Gesundheit des Unternehmens achten, müssen Sie auch zeigen, dass Sie sich an branchenübliche und behördliche Best Practices für die IT-Sicherheit halten und fundierte Entscheidungen auf lange Sicht treffen . Ein Cybersicherheits-Framework kann helfen.