Read about the latest cybersecurity news and get advice on third-party vendor risk management, reporting cybersecurity to the Board, managing cyber risks, benchmarking security performance, and more.
Insights blog.

Critical Vulnerabilities Discovered in Automated Tank Gauge Systems
Bitsight TRACE explores several critical vulnerabilities discovered in ATG systems and their inherent risk when exposed to the Internet.

What is information risk management? Learn more about how the classic equation of threat x vulnerability x consequence helps inform your cybersecurity risk management strategy.
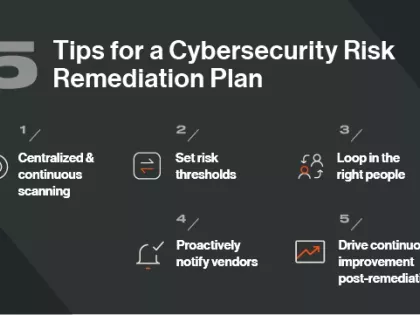
Does your organization have a cybersecurity risk remediation plan? Follow these 5 tips for crafting one.

Cyber risk mitigation and remediation are often talked about in the same terms. But they are different. Learn how you can optimize both.

Highlight cyber exposure management's role in risk control and urge collaboration between security experts and business leaders for improved cyber risk management.

Network security monitoring tools are a critical component of any IT security toolkit.

Compliance vs. Risk management. How your organization can unify its efforts to ensure cyber resilience.

As regulations shift and providers enter new markets, the telecom industry is changing rapidly. In preparation for these changes, telecom risk management professionals must become aware of new risks on the horizon. Privacy and net neutrality laws, new kinds of cyber threats, reputational dangers, and other factors are all poised to affect telecom companies deeply in 2019.

The term “digital resilience” has gained momentum over the past few years as cybersecurity threats have grown, but what does it really mean? And how can a company become digitally resilient?

Whaling attacks are a form of spear phishing that target senior executives. Learn how to defend against these attacks.

Executive performance and cyber risk management are now inextricably linked. Learn how CISOs can help executives be more accountable for cyber risk.

Enterprise risk management software helps businesses monitor, manage, and mitigate many types of risk. However, procuring and implementing ERM software requires a significant investment, and choosing the solutions that are right for your business is a perennial challenge for risk management professionals.

These are the basic steps you should take to develop an effective cyber risk management strategy.

What is a cybersecurity risk taxonomy and how can you use it to guide your organization’s security program and investments?

Our strategic direction is bolstered by an expanded partnership with Moody’s Corporation, enhanced Third-Party Vulnerability Detection & Response capabilities, and an improvement to our proprietary ratings algorithm.

New outsourcing opportunities may present as you build next year’s strategy, making Vendor Risk Management (VRM) critical for three main reasons.