Read about the latest cybersecurity news and get advice on third-party vendor risk management, reporting cybersecurity to the Board, managing cyber risks, benchmarking security performance, and more.
Insights blog.

Critical Vulnerabilities Discovered in Automated Tank Gauge Systems
Bitsight TRACE explores several critical vulnerabilities discovered in ATG systems and their inherent risk when exposed to the Internet.

Here are five questions you should ask yourself as part of your morning cybersecurity checklist that will help to protect your organization.

Read this blog to discover how tackling technical debt can transform your cybersecurity strategy, boost efficiency, and ensure compliance.

Every organization handles security differently, based on their needs and internal structure — but in some mid-sized and large companies, both the chief information officer (CIO) and the chief information security officer (CISO) are involved.
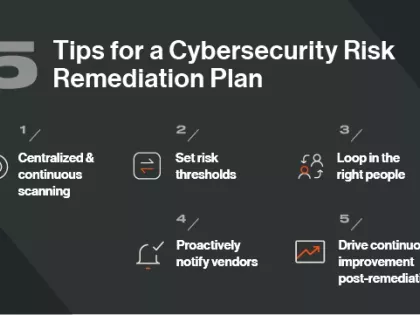
Does your organization have a cybersecurity risk remediation plan? Follow these 5 tips for crafting one.

Your attack surface is expanding everyday. Learn how external attack surface management can help you understand what you’re up against and inform remediation.

The Moody’s Analytics supply chain, credit, insurance, compliance and investment management offerings now feature Bitsight’s leading cyber risk analytics.

How is one questionnaire different from another, and how do you decide which ones to use in vendor risk assessments? We compare CAIQ vs. SIG.

As cyberattacks against cloud services and infrastructure increase, follow these best practices to improve your cloud security posture management.

We look at five ways you can reduce cyber threats without putting additional pressure on stretched resources.

Cybersecurity intelligence is a powerful weapon against risk. Learn how you can improve your cyber data collection, analysis, and sharing to mitigate emerging threats.

Cyber risk is now business risk and this means the role of the security risk management leader must be reframed. Learn how.

These are the basic steps you should take to develop an effective cyber risk management strategy.

Almost every day there seems to be another story about the “Internet of Things" (IoT). More and more “things” are being equipped to send and receive information over the internet. It might be fun to have your running shoes connecting to the cloud, but what does it mean, if anything, to your corporate network?

Discover the performance areas policymakers should begin measuring, why these are important and how they should collect the data.

From sensors on the factory floor to those that guide autonomous vehicles, the Internet of Things (IoT) is transforming how we live and work. Over the coming years, IoT will continue to change our world, with the number of connected devices expected to grow from 13.8 billion units in 2021 to 30.9 billion by 2025.